Zilliz Trust Center
Your trusted source for Zilliz’s security, privacy, and compliance commitments.
Attestations & Certifications
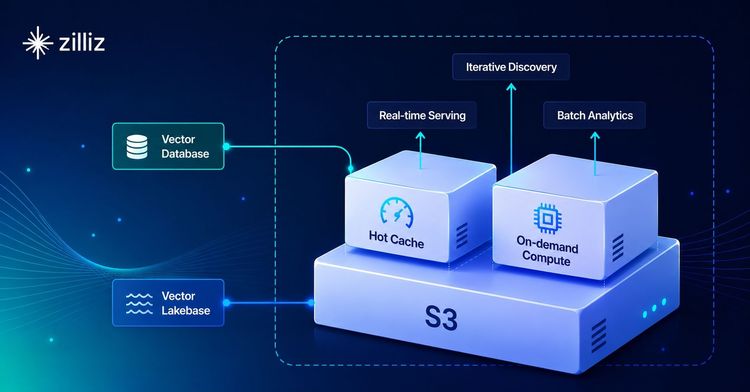
A fully managed cloud-native vector database designed for fast and easy AI-driven data processing.
Privacy & Data Protection Resources
Zilliz Cloud offers a comprehensive set of features to help users protect data privacy.
Key Features for Data Privacy Protection
Explore our key documents and statements related to data privacy, processing, and protection. Some resources may require an NDA for access—please contact us for more information.