Vector databases are fundamental to modern Enterprise AI search, enabling semantic understanding and fast retrieval of unstructured data through high-dimensional embeddings. The integration of vector databases into enterprise AI systems, which include applications like intelligent search, recommendation engines, and Retrieval Augmented Generation (RAG), necessitates robust security measures to protect sensitive corporate information. Enterprises deal with vast amounts of proprietary and confidential data, and any AI search solution must guarantee that this data remains secure throughout its lifecycle. Vector databases contribute to this by offering a suite of security features designed to prevent unauthorized access, maintain data integrity, and ensure compliance with regulatory standards. This "security-first" approach ensures that data protection is integrated into the search infrastructure from the ground up, rather than being an afterthought.
Specific security mechanisms employed by vector databases are crucial for safeguarding enterprise AI search. Data encryption is paramount, with data being encrypted both at rest (when stored) and in transit (when moving across networks). This typically involves industry-standard algorithms like AES-256, preventing unauthorized parties from reading sensitive data even if they gain access to the storage or network. Access control is another critical layer, implemented through Role-Based Access Control (RBAC) and strict permission management. RBAC ensures that users only have access to the data necessary for their tasks, aligning with the principle of least privilege. Authentication mechanisms such as Single Sign-On (SSO) and Multi-Factor Authentication (MFA) are also vital, verifying user identities before granting access to the vector database or AI applications. Furthermore, data isolation, often achieved through dedicated namespaces or Virtual Private Clouds (VPCs), prevents data leakage between different tenants or projects within the same infrastructure.
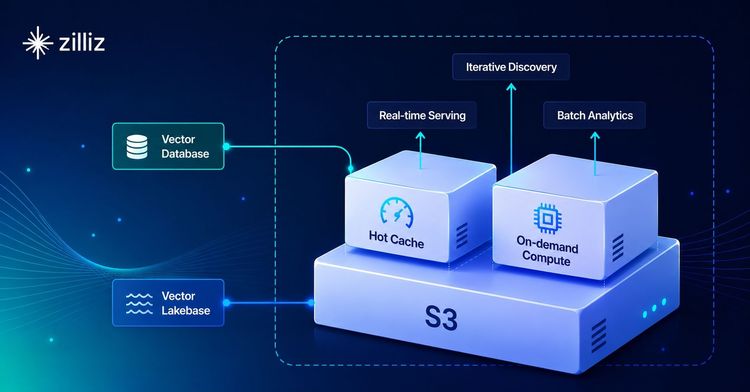
For enterprises deploying AI search, these security features are often managed and enhanced by platform providers. A vector database service like Zilliz Cloud incorporates a comprehensive security framework. Zilliz Cloud offers robust isolation and protection for clusters through dedicated namespaces and separate storage buckets, along with distinct VPCs for control and data planes. It utilizes OAuth0 for secure user authentication, supporting SSO and MFA, and provides granular, role-based access control with hierarchical permissions. Secure network access is ensured through IP allowlisting and Private Links, establishing secure connections between user VPCs and the Zilliz Cloud control plane. All data is encrypted at rest using AES-256 and in transit via HTTPS/gRPC with TLS 1.2+. Additionally, comprehensive audit logging and monitoring capabilities track activities, enabling detection of suspicious behaviors and ensuring compliance with regulations like GDPR, CCPA, and SOC 2. These integrated security measures allow enterprises to leverage the power of AI search while maintaining the confidentiality, integrity, and availability of their sensitive data.