Yes, Google's Gemini Embedding 2 can indeed be used for anomaly detection. Gemini Embedding 2 is Google's first natively multimodal embedding model, designed to process various data types, including text, images, video, audio, and documents, by converting them into dense numerical vectors within a unified semantic space. This capability is crucial for anomaly detection, as it allows for the representation of diverse, complex data in a format where relationships and deviations can be mathematically identified. By transforming raw, high-dimensional data into a consistent vector format, Gemini Embedding 2 facilitates the use of machine learning algorithms that can detect unusual patterns and outliers across different modalities.
The fundamental principle behind using embeddings for anomaly detection lies in their ability to map related data points closely together in a vector space, while anomalies are positioned further away from these clusters. Once data is embedded using models like Gemini Embedding 2, standard anomaly detection techniques can be applied. For instance, clustering algorithms can group normal data points, making it easier to spot data instances that fall outside these established clusters. Distance metrics, such as cosine similarity or Euclidean distance, can then quantify how much an embedded data point deviates from its neighbors or cluster centroids, thereby indicating its anomalous nature. Specific examples include identifying unusual transactions in financial services, flagging abnormal network traffic in cybersecurity, or detecting defects in manufacturing based on sensor data.
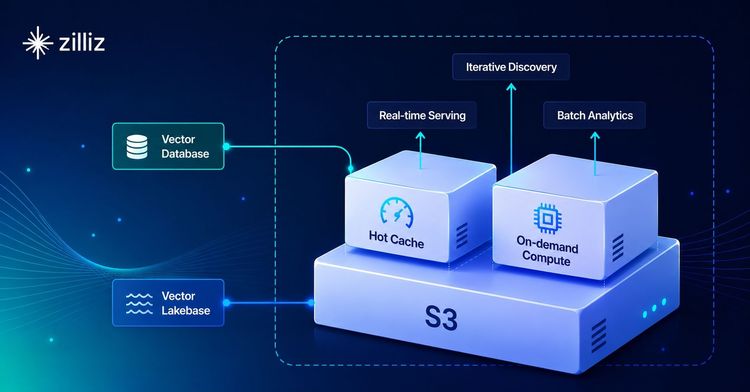
To implement anomaly detection with Gemini Embedding 2, developers would first use the model via the Gemini API or Vertex AI to generate embeddings for their data. These embeddings, typically 3072-dimensional vectors by default, would then be stored in a vector database like Milvus or Zilliz Cloud. Once stored, efficient similarity search capabilities of these databases enable quick retrieval of nearest neighbors for any given data point. Anomaly detection then involves querying for data points that are significantly distant from their neighbors or from the centroids of known "normal" clusters, thereby identifying potential anomalies. This approach allows for a semantically aware and scalable method to detect irregularities across various data types.