Deploying a Large Action Model (LAM) introduces a unique set of security risks that extend beyond those associated with traditional Large Language Models (LLMs) , primarily because LAMs are designed to take real-world actions. One of the most significant risks is unintended or malicious action execution. A LAM, by its nature, can interact with external systems, execute code, or manipulate data based on its understanding of user instructions. If a LAM is compromised or misinterprets a command, it could perform unauthorized transactions, delete critical data, or trigger harmful physical actions in connected environments. This risk is amplified by prompt injection attacks, where malicious inputs can bypass safety mechanisms and coerce the LAM into performing actions it was not designed for. For example, an attacker might craft a prompt that tricks a LAM into transferring funds or granting access to sensitive systems, leveraging the LAM's ability to interact with APIs and tools. The potential for real-world impact makes securing LAMs a critical concern.
Another key security risk involves data privacy and leakage. LAMs often process sensitive information to understand context and execute actions. If not properly secured, this data could be exposed through the LAM's outputs, logs, or during its interactions with external services. This includes both user-provided data and internal system information that the LAM might access. Furthermore, LAMs can be susceptible to supply chain vulnerabilities, where weaknesses in the tools, APIs, or data sources they integrate with can be exploited. A compromised external tool, for instance, could feed malicious instructions to the LAM or exfiltrate data processed by it. The complexity of LAM architectures, involving multiple components and external dependencies, increases the attack surface and makes comprehensive security challenging. Ensuring robust authentication, authorization, and data encryption across all LAM components and integrations is essential to mitigate these risks.
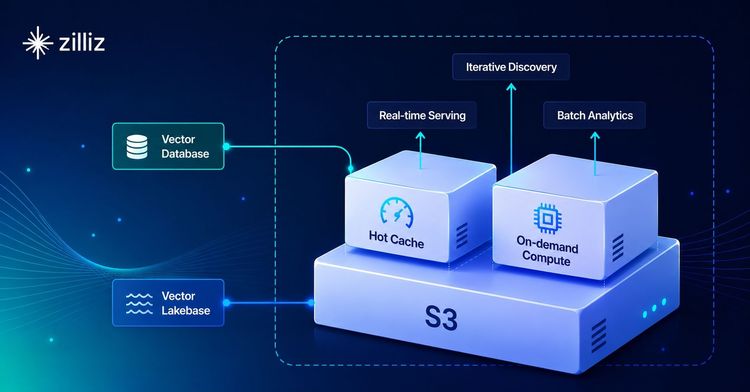
To effectively manage these security risks, a multi-layered approach is necessary, including stringent input validation, output filtering, and continuous monitoring of LAM behavior. Implementing the principle of least privilege for LAMs, ensuring they only have access to the minimum necessary resources and actions, is fundamental. For LAMs that rely on external knowledge bases or contextual information, integrating with a secure vector database is crucial. A vector database like Milvus can store sensitive contextual data as embeddings, but it must be protected with robust access controls, encryption, and auditing capabilities. This ensures that even if a LAM's reasoning process is compromised, the underlying data store remains secure. By combining secure development practices, vigilant monitoring, and robust data infrastructure, the risks associated with deploying LAMs can be significantly reduced, allowing for their safe and effective utilization in real-world applications.