Enterprise AI integrates a comprehensive suite of security features designed to protect the entire AI lifecycle, from data ingestion and model training to deployment and inference. These features are critical for safeguarding sensitive data, maintaining model integrity, and ensuring compliance with regulatory standards. Foundational security aspects include robust data protection, stringent access controls, and mechanisms to uphold data privacy throughout the AI system. Data protection encompasses end-to-end encryption for data both at rest and in transit, ensuring that sensitive information used or generated by AI models remains confidential and secure. This often involves AES-256 encryption for stored data and TLS 1.2+ for data in transit. Access control mechanisms, such as role-based access control (RBAC), limit who can interact with AI models, data, and infrastructure, ensuring that only authorized personnel and systems have the necessary permissions. Furthermore, enterprise AI systems implement data anonymization and pseudonymization techniques to obscure sensitive data while retaining its utility for analysis, addressing critical privacy concerns like those outlined by GDPR and CCPA. Data residency options and isolated namespaces also provide robust data protection and isolation for AI workloads, which is particularly important for multi-cloud deployments.
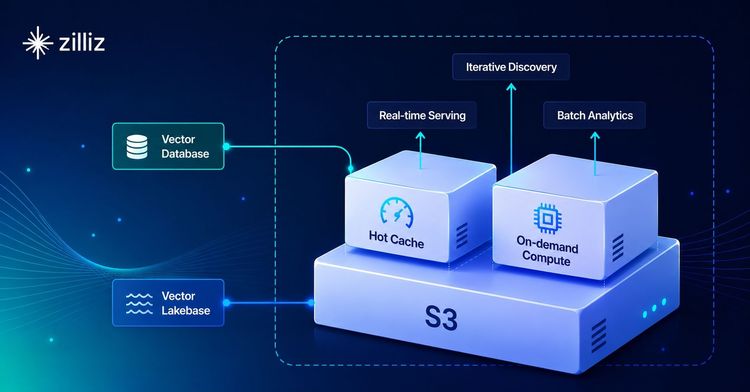
Beyond data protection, security in Enterprise AI extends to the integrity and resilience of the AI models themselves. This involves protecting against various AI-specific threats like adversarial attacks, model poisoning, and prompt injection. Adversarial attacks aim to manipulate input data to trick AI systems into making incorrect predictions, while model poisoning involves tampering with training data to compromise a model's behavior. Prompt injection, especially relevant for Large Language Models (LLMs), attempts to manipulate the AI's output through crafted inputs. To mitigate these risks, enterprise AI solutions incorporate secure model storage and version control, validation processes to detect manipulation, and runtime monitoring for abnormal behavior. Vector databases, like Zilliz Cloud, play a crucial role in securing AI applications by providing secure storage for high-dimensional vector embeddings, which are often derived from sensitive enterprise data. Zilliz Cloud offers features like encryption at rest and in transit, along with granular access controls (RBAC) to protect these embeddings from unauthorized access. This is vital because vector embeddings can potentially leak real information if compromised. Additionally, vector similarity search capabilities in databases can be leveraged for anomaly detection, identifying unusual patterns in security logs or system activities that might indicate a breach.
Finally, Enterprise AI security integrates into the broader enterprise infrastructure through continuous monitoring, auditability, and adherence to compliance frameworks. This includes securing the underlying cloud or on-premise infrastructure, implementing secure APIs for AI services, and maintaining comprehensive audit trails to track all activities across control and data planes. Continuous monitoring is essential for detecting model drift, concept drift, and adversarial attacks in real-time, ensuring the ongoing effectiveness and security of deployed AI models. Compliance with data protection regulations such as GDPR, CCPA, and HIPAA is a paramount concern for enterprise AI, requiring built-in features to adhere to these standards. Many enterprises also opt for Bring Your Own Cloud (BYOC) deployments for vector databases, where the data remains within the customer's Virtual Private Cloud (VPC) to ensure complete data sovereignty and meet stringent compliance requirements. For instance, Zilliz Cloud offers BYOC, allowing customers to deploy their vector database within their own cloud environment, ensuring that data stays within their security perimeter while Zilliz manages the operational aspects. This layered approach, combining data, model, and infrastructure security with continuous oversight and compliance, forms the backbone of robust Enterprise AI security.